Looking to gain insight into public attitudes toward parking payment and enforcement systems, the mystery shopping company Servimer recently surveyed more than 2,100 drivers. They found that drivers want flexibility, transparency, and reassurance more than speed or innovation.
Issues

Current Month's Issue

Last Month's Issue
Buyer's Guide
Latest Articles
Drawing on Parker Technology's 2025 Consumer Data Report and its 2026 artificial intelligence (AI) perception survey, the authors make the case for what good technology strategy actually looks like in a parking environment. The short version: It is not tech versus people. It never was.
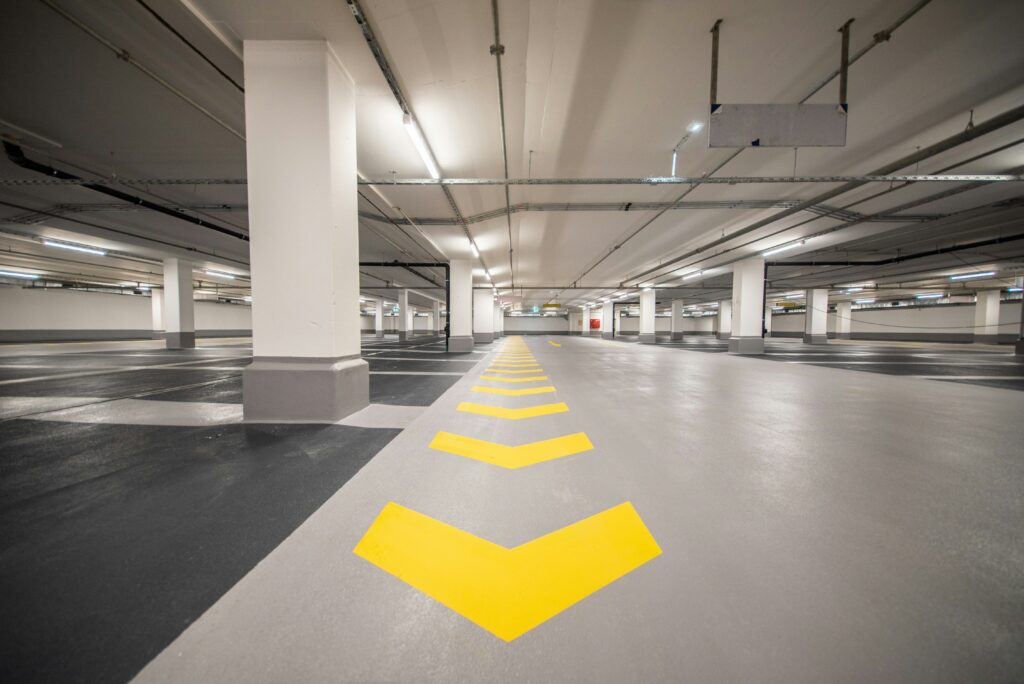
Across the U.S., parking facilities built in the 1970s and 1980s are now reaching a critical inflection point. Today, many of these structures are approaching or exceeding their intended 50-year lifespan, forcing owners to confront a fundamental question: repair, retrofit, or replace?
On June 1, Safe Park Indy (SPI), Indianapolis’s vehicular homelessness parking program, resumed operations after a yearlong hiatus. Known as Safe Park Indy 2.0, the new, improved model is designed with flexibility and automation to better meet the community’s needs and reduce the program’s labor requirements.
Among the first class of honorees inducted into the Parking Hall of Fame, Mary S. Smith has enjoyed a distinguished 50-year career in parking.
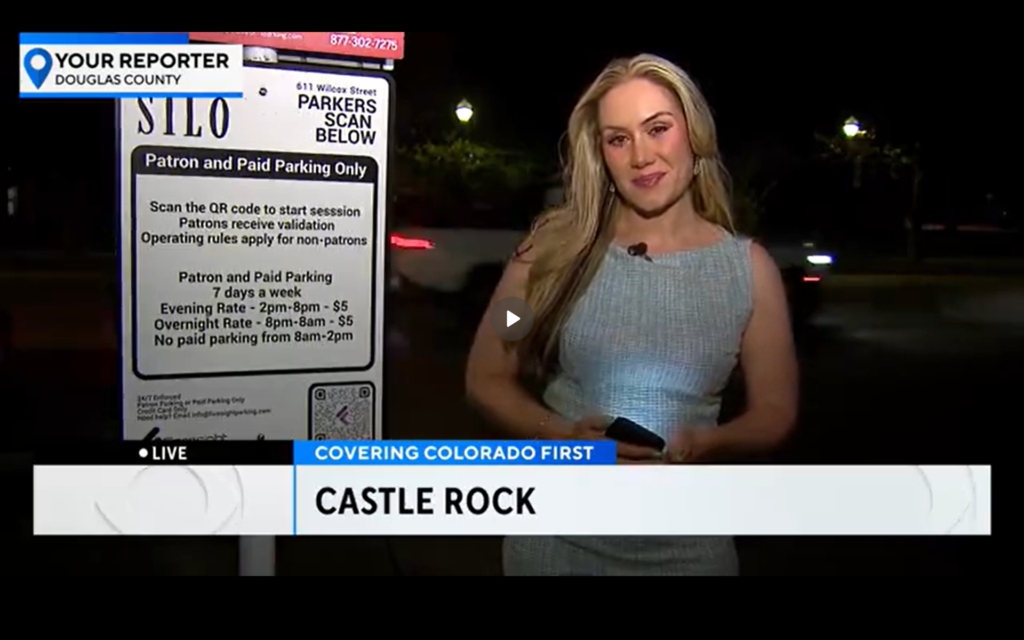
Arrive and Flash, two of the parking industry's largest technology players, have begun to offer automatic access and payment capabilities to off-street parking facilities across the United States, beginning in Philadelphia.
Human trafficking is real, but fear-driven narratives about our environments do not reflect how it actually operates. Leading responsibly on trafficking does not require expanding our mission. It requires discipline.
Issues

Current Month's Issue

Last Month's Issue